Why Deep Packet Inspection Falls Short
Malicious content and attacks are evolving at the same time network traffic is increasing in both volume and complexity; the combination of the two has put traditional network filtering technologies at risk. One in every 14 downloads currently contains malicious content that may jeopardize reputation- and customer-relationship management as well as creating operational challenges.
According to PwC’s 2012 Global State of Information Security Survey, only 43 percent of security experts believe their information security strategies are up to par. Organizations are susceptible to information leakage and possible IT infrastructure damage when malicious content and non-compliant data pass through the networks undetected.
Advanced security practices are needed to combat the increase in security threats that have emerged due to social media, mobile-data usage and cloud computing. Conventional inspection technologies used to secure the network at the packet level, such as Deep Packet Inspection (DPI) and packet filtering, are only marginally efficient, and they are unable to scale to provide safe usage of the advancing Internet.
The Limitations
DPI currently is the most widespread tool used for handling network packet data. It functions by comparing the IP packet sequences against known offending patterns. To be effective, DPI systems match the packet information to these patterns in real time, which imposes two main limitations:
There are only so many packets a DPI tool can hold at a time for pattern matching. The amount of IP packets needed to transmit an application payload often exceeds the number of packets that a DPI system can inspect at a time. As a result, malware embedded in large application payloads will pass through.
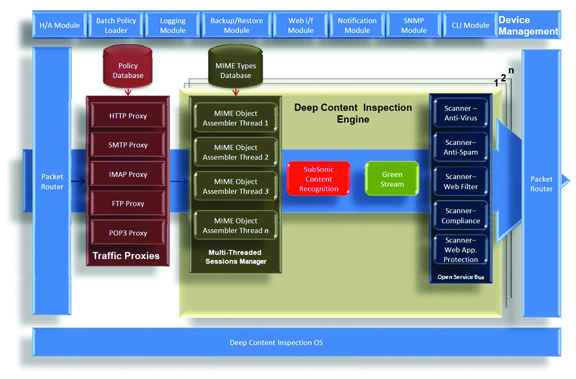 |
| FIGURE 1: Deep Content Inspection Overview |
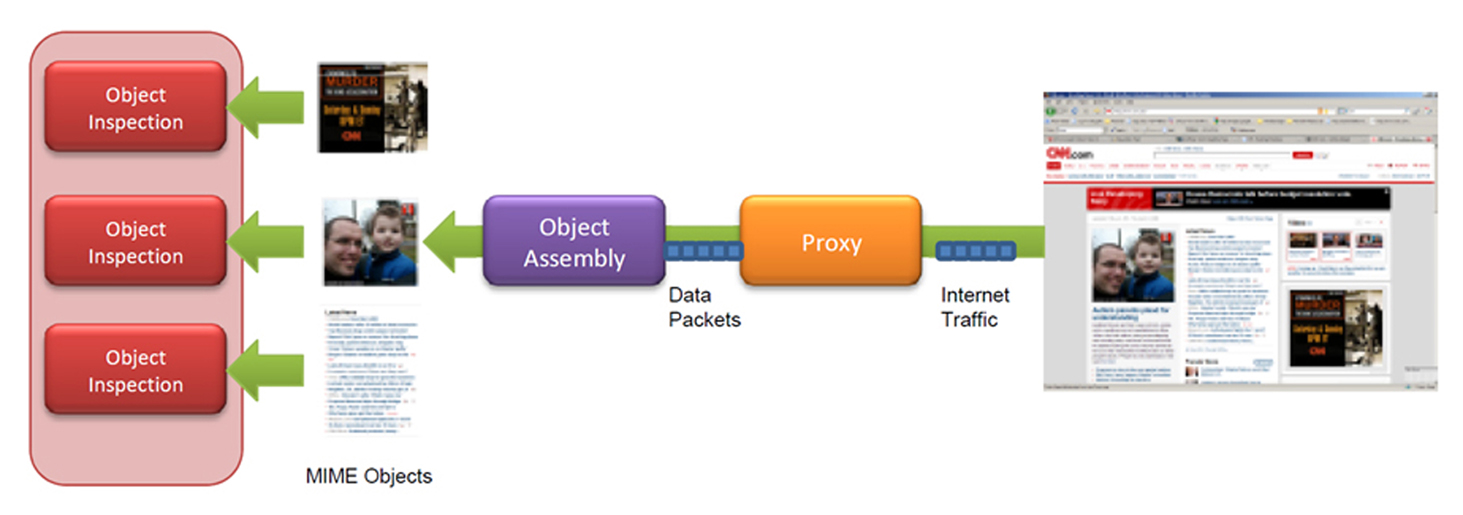 |
| FIGURE 2: Deep Content Inspection In UseSurvey Sez: Wireless Will Drive DPI |
Real-time DPI has limited memory available for pattern matches. Packet data obtained from a DPI system must be paired with a known malware threat, but the amount of unique signatures available for the system to match against is restricted.
The limitations of DPI are preventing organizations from achieving optimal network security. The growing number of unsupported application types as well as nested, zipped or archived files can take advantage of these limitations and pass through a DPI system that isn’t qualified to handle them, thus sneaking onto the network.
A Step Forward
A new approach to data inspection that incorporates thorough analysis is critical to address the undetected and emerging threats. Deep Content Inspection (DCI) is an advanced and comprehensive form of network filtering that works as a fully transparent device.
A DCI solution can examine the entire object and detect any malicious or non-compliant intent, while DPI only checks the body or header of data packets passing through a network. DCI reassembles, decompresses and/or decodes network traffic packets into their constituting application level objects, also called MIME objects.
DCI is able to recognize the intent of data-in-motion because the full content-based inspection is able to perform in real time. This allows DCI to inspect at a much broader scope than would be available by solely matching packet sequences against patterns. DCI also executes a reputation search-and-behavior analysis on structured or packed data, providing a whole new level of protection. DCI can find and assess signatures that cross packet boundaries by keeping track of content across multiple packets.
By veering away from traditional packet review and concentrating on the content and intent of data, DCI offers a complete method for screening and preventing attacks and malicious content.
Dr. Hongwen Zhang is president and CEO at Wedge Networks. Contact him at info@wedgenetworks.com.